Services
- Brightwave
- Services

Our Best Service
IT SECURITY SERVICES

Penetration Testing
Simulated Adversarial Attacks to Validate Defensive Effectiveness
Our penetration testing services employ sophisticated attack simulations mirroring real-world adversary techniques. We conduct external, internal, wireless, and social engineering tests using manual techniques combined with advanced tooling to identify exploitable vulnerabilities before malicious actors can discover them.
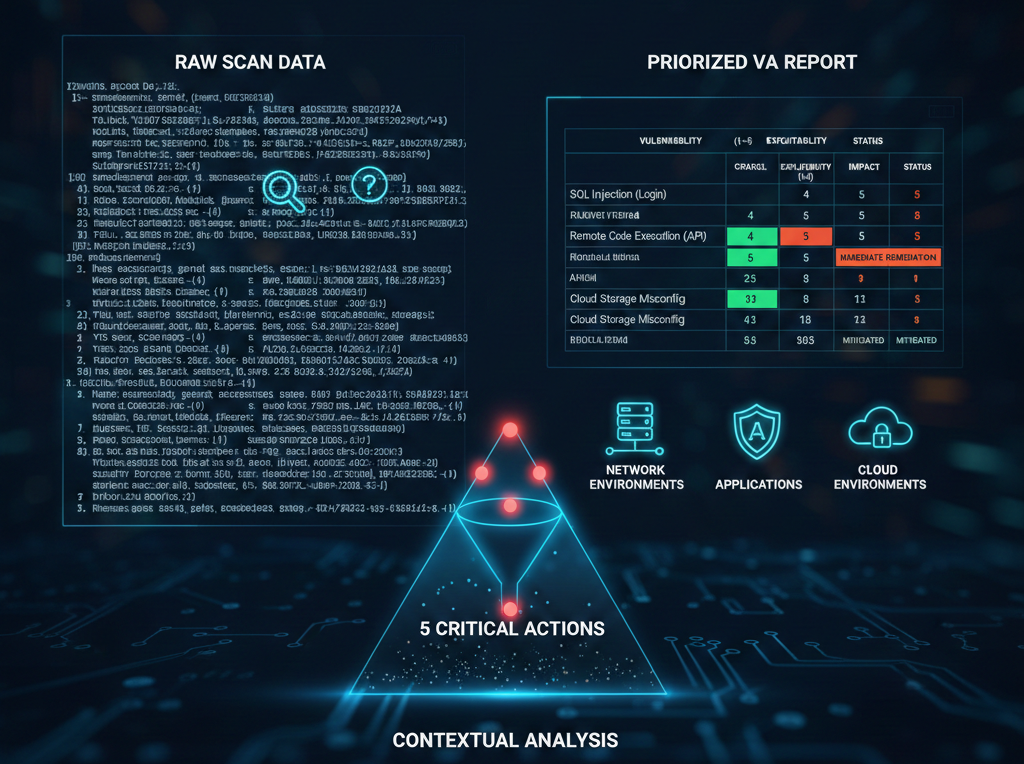
Vulnerability Assessment (VA)
Systematic Identification and Prioritization of Security Gaps
Moving beyond simple scanning, our vulnerability assessments provide contextual analysis based on exploitability, potential impact, and existing controls. We conduct authenticated and unauthenticated scans across networks, applications, and cloud environments.

Security Audit & Compliance Assessment
Validating Security Posture Against Standards and Regulations
Our security audits provide independent validation against industry standards (OWASP, NIST, ISO 27001), regulatory requirements (PCI DSS, HIPAA, GDPR), and organizational policies. We conduct control testing, evidence collection, gap analysis, and maturity assessment.
%20Services.png)
Security Operations Center (SOC) Services
*24/7 Threat Monitoring, Detection, and Response*
Our SOC services provide continuous security monitoring, threat detection, incident response, and threat hunting through a combination of advanced technology and human expertise. Services include log management, SIEM deployment, endpoint detection, and threat intelligence integration.
.png)
Cyber Threat Intelligence (CTI)
Proactive Threat Anticipation and Strategic Defense Planning
Our CTI services help organizations move from reactive security to proactive threat anticipation through collection, analysis, and dissemination of threat intelligence specific to your industry and technology environment.

Security Training & Awareness Programs
Building Human Firewalls Through Education and Engagement
We develop customized security awareness programs addressing organization-specific risks, compliance requirements, and cultural contexts. Programs include phishing simulations, interactive training modules, and measurement frameworks.

Digital Forensics & Incident Response
Rapid Investigation and Recovery Following Security Incidents
When security incidents occur, our team provides rapid containment, investigation, and recovery services to minimize business impact, supporting both technical remediation and legal/regulatory requirements.

Cyber Consulting & Strategy Services
Strategic Guidance for Security Program Development and Maturity
Our consulting services help organizations develop, implement, and mature comprehensive cybersecurity programs aligned with business objectives, including security strategy, risk assessment, architecture design, and third-party risk management.

Secure Development Services
Integrating Security Throughout the Software Development Lifecycle
We embed security practices into every phase of the SDLC, from requirements and design through deployment and maintenance, including threat modeling, secure code review, and security testing integration into CI/CD pipelines.

Managed Security Services
Comprehensive Security Management for Continuous Protection
For organizations seeking to outsource security operations, our managed services provide ongoing vulnerability management, patch management, configuration management, security tool administration, and periodic assessments.
